by
John R. Fischer, Senior Reporter | April 29, 2019
A design flaw in the DICOM standard
risks malware infiltration that could
negatively affect medical image storing
and sharing
A design flaw in the DICOM standard has raised a number of potential red flags on the security around the storage and exchange of medical images.
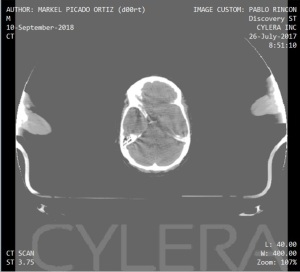
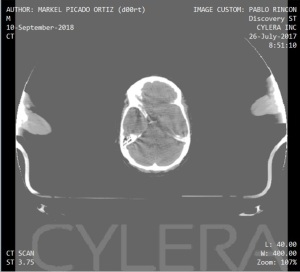
Uncovered by Markel Picado Ortiz, a researcher for medical device cybersecurity firm Cylera, the deficiency enables hackers to embed executable codes of malware within DICOM files to create PE/DICOM files, hybrids that are fully-functioning, Windows executable and specification-compliant DICOM images that can be opened and viewed in any traditional DICOM viewer. Such an addition raises the risk for potential evasion and multistage attacks, with attempts to reduce or eliminate the malware resulting in damages to the quality and the release of protected health patient information.
"Cyber threats in healthcare should be viewed through the lens of patient safety and clinical continuity,” Paul Bakoyiannis, chief technology officer for Cylera, told HCB News. “We must be aware that mitigation steps could have harmful side effects due to the sensitivity of the data found within healthcare systems, and the importance of uptime. Complex dynamics arise when cyber attacks and clinical care are mixed, as these findings show, and healthcare organizations should be aware of the impacts of both the threats themselves and the attempted remediation steps.”



Ad Statistics
Times Displayed: 5811
Times Visited: 19 Brand-New FDA-cleared Advanced Ultrasound Medical Device available for sale or lease to Wound Care Centers or any other Medical Facilities.The Arobella 1000D is designed for non-contact or debridement ultrasound wound healing therapy, or any other wounds
Comprising the header of the DICOM file format standard is the Preamble, a 128-byte section at the beginning of the file that facilitates access to the images and metadata within the DICOM image. As any random sequence of 128 or fewer bytes can be inserted within the preamble without jeopardizing the image file’s conformance with the DICOM standard, third parties can establish compatibility with non-DICOM image viewers for formats such as JPG and TIFF images, without having to worry about structural requirements.
Attackers, however, can exploit this feature by inserting full PE headers that make the DICOM file appear to be an executable. They also can fully embed a functioning executable into a DICOM image, while maintaining its ability to be executed by the operating system and act as a standards-compliant DICOM image file, thereby allowing the executable file to appear as a DICOM image, a reversal of the true standard which makes DICOM files appear as other formats.
In doing so, the malware can grow into more potent variants that infect and use patient data to hide, protect and spread itself. It is able to evade detection from automated mechanisms in configurations such as A/V software by being executed without changing the ".dcm" file extension and by maintaining the integrity of the DICOM format.